From: Office of Information Technology
Sent: Tuesday, March 31, 2020
To: Faculty and Staff
Subject: Video-Teleconferencing Hijacking Advisory

Dear Faculty and Staff:
There are reports of video-teleconferencing being disrupted by pornographic and/or hate images and threatening language. These are known as VTC hijacking (Also called “Zoom-bombing”). As individuals continue the transition to online lessons and meetings, The OIT Information Security Office recommends exercising due diligence and caution in your cybersecurity efforts.
You can follow the recommendations from this blog, How to Keep the Party Crashers from Crashing Your Zoom Event, that describes how to manage screen sharing, manage participants and waiting room.
We are also including the following steps to mitigate teleconference hijacking threats:
- Do not share a link to a teleconference or classroom on an unrestricted publicly available social media post. Provide the link directly to specific people.
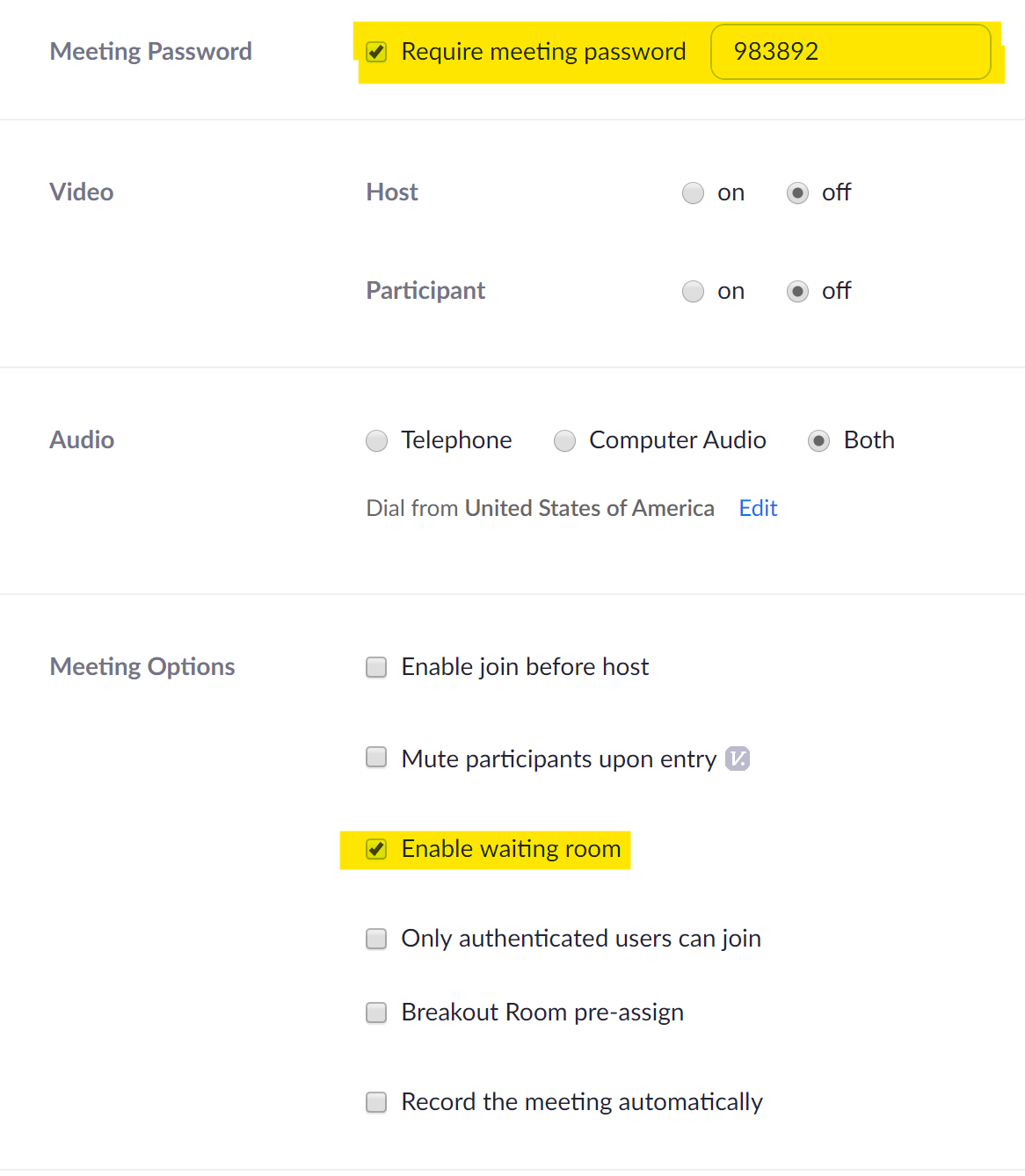
- Do not make meetings or classrooms public. In Zoom, there are two options to make a meeting private: require a meeting password or use the waiting room feature and control the admittance of guests
- Manage screensharing options. In Zoom, change screensharing to “Host Only.”

- Ensure users are using the updated version of remote access/meeting applications. In January 2020, Zoom updated their software. In their security update, the teleconference software provider added passwords by default for meetings and disabled the ability to randomly scan for meetings to join.
If you were a victim of a teleconference hijacking, please report it to the Office of Information Security ( [email protected] ) and we will guide you through the process and next necessary steps.
Last Updated: 04/01/2024 10:18